Accepted for publication in the Journal of Intelligent Information Systems
Journal
Research in neural generative models for dynamic networks is constantly evolving,
and sophisticated solutions have been exploited to characterize the long-term evolution of temporal graphs.
Despite the efforts in the literature, state-of-the-art models face the problem of handling changes
in the graph structure by relying on prior knowledge, compromising the model’s flexibility.
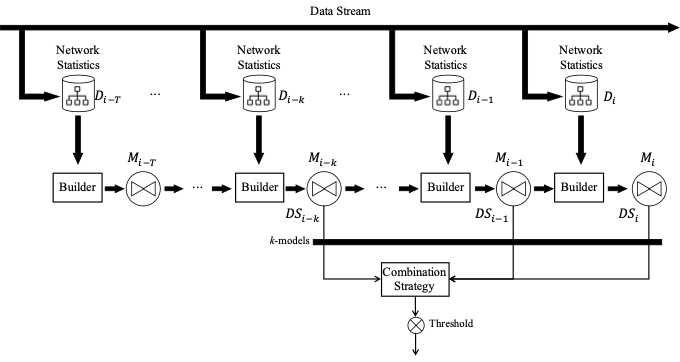
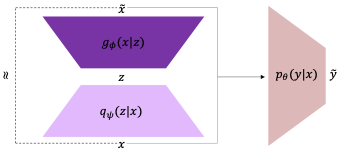
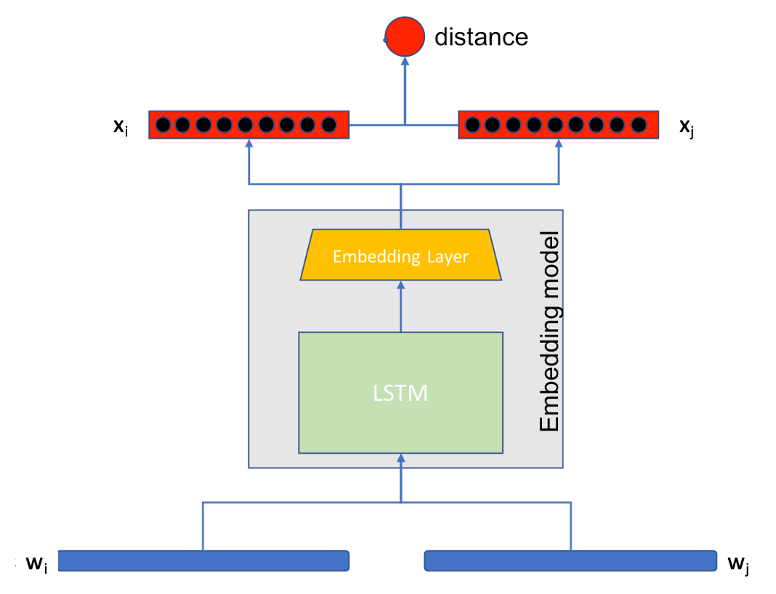
In this paper, we propose a graph-size invariant probabilistic generative model,
named FuDGE, Fully Dynamic Graph Evolution, for predicting the graph evolution through step-wise changes
in the graph structure. FuDGE can generate evolving graphs by exploring the whole node space,
thus ensuring fast and effective generation.
We evaluate FuDGE on real and synthetic benchmark datasets and compare its performance against state-of-the-art
competitors. The results demonstrate that our approach offers a competitive advantage in generation and
prediction quality compared to existing literature.
Read more